
1/22/26
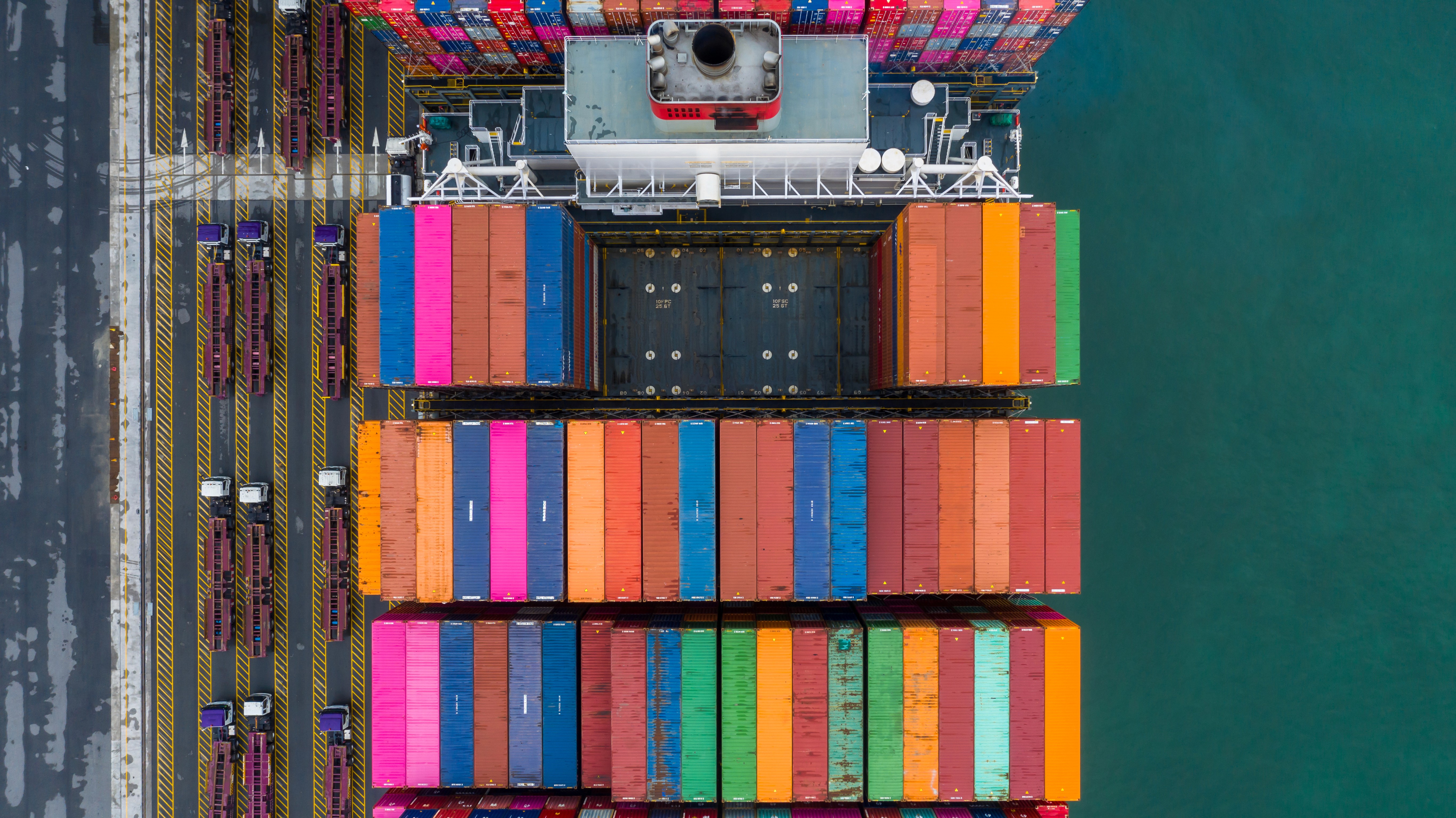
Supply Chain Management and Logistics in the Crosshairs of Cybersecurity Threats
Cybersecurity threats targeting supply chain management and logistics are rising sharply due to expanded digital connectivity, increased reliance on third parties, and vulnerabilities in IoT and cloud systems.
Modern supply chains are complex ecosystems involving numerous stakeholders, from raw material suppliers and manufacturers to logistics providers, distributors, and retailers. This complexity creates a wide attack surface for cybercriminals. According to industry guidance, vulnerabilities in information systems and inadequate monitoring of suppliers can compromise product quality, introduce compromised hardware or software into the chain, and expose intellectual property to misuse. These concerns highlight that supply chains are not only operational systems but also critical cybersecurity risk domains.

Cybersecurity challenges in supply chain management and logistics take many forms. Malware, phishing, ransomware, and unauthorized access are persistent threats. Malware can spread through vulnerable supplier systems, disrupting internal operations and exposing sensitive data. Ransomware attacks, in particular, are a major concern. They can encrypt critical logistics systems, paralyzing operations and demanding payment to restore access.
A significant dimension of the risk stems from the adoption of new technologies such as IoT devices and cloud computing. While these technologies improve efficiency and real time visibility, they also expand the number of entry points for attackers. IoT sensors monitoring inventory or controlling automated processes may lack robust security features, allowing attackers to pivot from peripheral systems into core infrastructure. Cloud platforms, if misconfigured, can lead to data breaches and unauthorized access to shared applications or APIs.
Even beyond digital systems, physical crime with a cyber dimension is rising. Cybersecurity firms have found that hackers are increasingly “teaming up with crime rings to hijack cargo,” using phishing and social engineering to access internal systems and reroute shipments for theft. This coupling of cyber and physical threats highlights the convergence of digital intrusion with tangible loss in logistics operations.
High profile supply chain disruptions illustrate how deep these risks run. Attacks on suppliers or logistics platforms can leave retail shelves bare, delay deliveries of essential goods, and create operational havoc. For example, a cyberattack against a major food distributor disrupted deliveries to thousands of grocery stores, leading to “temporary supply challenges” for retailers and signaling how deeply cyber incidents can affect physical supply chains.
Compounding the problem is the fact that supply chain ecosystems are often geographically widespread and involve many smaller partners with varying levels of security maturity. Coordinating consistent cybersecurity practices across tiers of suppliers presents logistical and organizational challenges. The attack surface increases with each partner, and attackers routinely exploit third party vulnerabilities to move laterally into larger networks.
Managing data integrity is another critical issue. Supply chain data such as tracking information, manifests, or inventory records can be tampered with or corrupted, leading to operational inefficiencies, incorrect shipments, and financial loss. Malicious actors may manipulate data for financial gain, sabotage, or espionage, undermining confidence in shared information across partners.
Cybersecurity experts and industry leaders emphasize the importance of proactive risk management. The president of Exiger, Carrie Wibben Kaupp, has stated that “Supply chain intelligence is no longer ‘an economic nice to have’… today, it’s ‘a national security imperative.’” Her perspective reflects the growing recognition that supply chain risks intersect with broader economic and geopolitical concerns.
Addressing these challenges requires a multi layered approach. Organizations must evaluate vendor security practices, conduct thorough third party risk assessments, monitor systems continuously, and implement secure access controls and encryption. A robust cybersecurity strategy must also incorporate visibility into connected devices, cloud platforms, and partner networks. These measures help reduce the likelihood of breaches while enabling faster detection and response when attacks occur.
“Supply chain intelligence is no longer ‘an economic nice to have’… today, it’s ‘a national security imperative.’” - Carrie Wibben Kaupp, President of Exiger
Emerging technologies such as artificial intelligence and machine learning can support predictive risk analysis and anomaly detection across supply chain systems. These tools help identify patterns of unusual behavior that may indicate early stages of compromise. In addition, creating a culture of security awareness, where employees are trained to recognize phishing attempts and adhere to best cybersecurity practices, strengthens defenses against social engineering and insider threats.
Ultimately, supply chains are only as secure as their weakest link. A breach at one supplier can propagate downstream, disrupting partners and customers alike. As global supply networks grow in scale and interconnection, cybersecurity must be integrated at every level of planning and operation. Organizations that treat supply chain security as a strategic priority rather than a technical afterthought will be better equipped to protect their networks, assets, and reputation.
ready to secure your data?


